Dive into the Cyber threat landscape in the aviation industry 2023


Julien D. est analyste de la menace cyber depuis juin 2022, chez Sysdream, la division cybersécurité de Hub One. Comme tant d’autres de ses collègues, pour Julien, la cybersécurité est plus qu’un travail, c’est une véritable passion ! A tel point que Julien décide d’approfondir le sujet en s’intéressant à la psychologie des acteurs malveillants pour comprendre leurs comportements. Formé en intelligence économique, Julien se concentre surtout aujourd’hui sur la protection de l’information des organisations. Pour mieux appréhender ce volet défensif, Julien approfondit ses connaissances en s’intéressant aux sujets politiques, culturels et géoéconomiques, qui lui permettent d’avoir une vision globale des faits de société et de mieux appréhender les potentielles intrusions. Côté technologique, avec Julien, nous ne sommes jamais loin de son métier puisque son attrait va pour le logiciel Maltego, un outil de collecte d’informations qui permet l’exploration de données sur un sujet choisi. On ne se refait pas !
As technology becomes increasingly integrated into the aviation sector, it becomes imperative for industry stakeholders to prioritize cybersecurity measures. In France, where airlines operate within a complex environment entwining economic, regulatory, and geopolitical considerations, vigilance against cyber threats becomes of crucial importance.
On the geopolitical front, state-sponsored cyberattacks raise growing concerns due to their potential harm, driven by their sophistication and resources. Economically, cost-cutting pressures may lead aviation industry players to invest in less secure or reliable technologies. The growing complexity of aviation technology also makes it challenging for organizations to stay informed about the latest cybersecurity threats and vulnerabilities.
Moreover, the continually evolving legislative landscape around cybersecurity aims to protect citizens and organizations from cyberattacks. As operators of essential services, aviation industry players must comply with security rules defined by the NIS Directive since 2018, and NIS 2 since 2023, ensuring the governance, protection, and defense of their information networks and systems. This compliance involves obligations such as maintaining a list of their information networks and systems and undergoing checks by ANSSI.
Similarly, the General Data Protection Regulation (GDPR) that came into effect in 2018 places the responsibility on aviation sector organizations to protect personal data, obliging them to notify their national data protection authority of breaches within a set timeframe (e.g., 72 hours for CNIL in France). GDPR advocates for inventorying access to the organization, connections with external entities, and regularly updating these inventories to identify points of security.
To anticipate cybersecurity risks, it is essential to adopt a proactive approach by raising awareness of threats and mitigating risks. This involves implementing technical measures such as firewalls, antivirus software, and data backups, as well as the rigorous application of processes and procedures subjected to regular testing. Additionally, staying informed about the latest threats specific to the aviation sector helps strengthen the organization’s protection capabilities.
Analysis of the figures recorded by CERT-SysDream on the aviation sector in 2023
764 cyber attacks recorded in the aviation sector in 2023
During the year 2023, the in-depth analysis of data related to cyberattacks targeting the aviation sector reveals intriguing trends and significant monthly variations. In January, the sector recorded 10 incidents, marking a relatively calm start to the year. However, this tranquility was quickly disrupted, with a notable increase in February (82) and March (91), suggesting an intensification of malicious activities. The months of April, May, and June maintained some stability, although the number of attacks slightly decreased in June (63). The summer period was characterized by a continuous decline, with 64 attacks in July, 62 in August, and 60 in September. However, the last quarter of the year saw a gradual increase, with a peak in October (74) followed by a slight decrease in November (41) and December (43).

Among these 764 cyberattacks recorded in the aviation sector in 2023, we can predominantly categorize them into two types: Distributed Denial of Service (DDoS) attacks and ransomware attacks, as indicated by these figures:

- Distributed Denial of Service (DDoS) Attacks: 679 attacks
The detailed figures clearly indicate that Distributed Denial of Service (DDoS) attacks constituted the overwhelming majority of incidents, totaling 679 cases. These attacks aim to overwhelm the computer systems of airlines by saturating their servers with traffic, thereby impeding the availability of services. The scale of these attacks underscores the critical need for stakeholders in the aviation sector to strengthen their defenses against DDoS assaults to maintain smooth and secure operations.
- Ransomware Attacks: 52 attacks
The 52 ransomware attacks pose a significant threat to the aviation sector. Cybercriminals use malicious software to encrypt sensitive data of airlines, subsequently demanding a ransom payment in exchange for the release of the information. At the end of May 2023, a security vulnerability (CVE-2023-34362) was identified in Progress Software’s MOVEit product. This flaw was exploited by numerous malicious actors, granting them unauthorized access to sensitive data, and the aviation sector was not spared from this.
These attacks have serious implications, not only in terms of operational disruption but also substantial financial risks, not to mention the loss of trust with users of various airlines or aviation companies and their clients. The highly strategic and sensitive nature of data in the aviation sector makes it a prime target for ransomware attacks.
The main targets are airports: 486 out of 764, or 64%
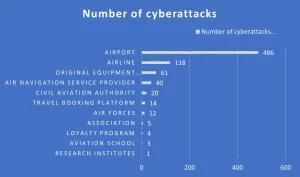
The analysis of specific targets of cyberattacks against the aviation sector in 2023 highlights a significant concentration on key entities. The results reveal that airports were the predominant targets, recording a total of 486 attacks out of the 764 documented, representing 64% of the total.
A thorough examination of the main targets of cyberattacks in the aviation sector in 2023 provides a symbolic and strategic insight into attackers’ motivations. Airports, as crucial hubs of air transportation, represent more than just physical infrastructure. They symbolize global connectivity and mobility, making them prime targets for attackers seeking to destabilize, erode confidence, or exert geopolitical pressure.
Airlines, as essential players in the transport of people and goods across borders, are strategic targets for attackers aiming to steal specific individuals’ data.
Original equipment manufacturers, with their crucial role in the design and production of aerospace technologies, are an attractive target for those seeking to disrupt supply chains or steal intellectual property data, as observed by CERT-SysDream during various campaigns in the aviation sector throughout 2023.
The primary type of attack is DDoS: 679 out of 764, or 89%
Data analysis reveals that ransomware and Distributed Denial of Service (DDoS) attacks dominate the landscape of cyberattacks in the aviation sector in 2023 due to specific motivations and consequences.
Ransomware attacks (52) are particularly widespread due to their potential profitability for cybercriminals. By targeting entities in the aviation sector, attackers seek to paralyze critical operations by encrypting data and demanding substantial ransoms. The devastating financial and operational consequences encourage malicious actors to exploit this lucrative method, jeopardizing the continuity of aviation operations.
DDoS attacks (679) are favored for their ability to disrupt operations massively and « easily. » They are easily executable and create a considerable disturbance, making them attractive for small groups seeking rapid destabilization and attention. The actors behind these attacks sometimes aim to overwhelm specific infrastructures, causing downtime, flight delays, and operational disruptions.
Victimology
- The primary victim country is Sweden: 64 attacks
- France is the second most affected country: 56 attacks
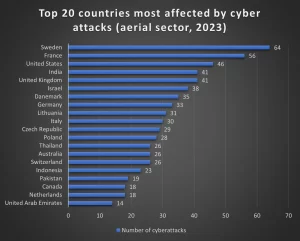
The analysis of the most targeted countries in cyberattacks within the aviation sector in 2023 reveals a multidimensional complexity. Sweden, being the most targeted country with 64 attacks in 2023, can be perceived as a preferred target due to its neutral position, making it strategically important for actors seeking to destabilize Europe. A significant portion of the attacks on Sweden is also linked to a blasphemous provocation in June 2023, provoking retaliation from several cybercriminal groups towards Swedish websites.
France, with 56 attacks, reflects a similar trend, being a key player in NATO and having significant influence in global geopolitics, particularly with the military aid it has provided to Ukraine.
The United States, the United Kingdom, India, and Israel, all targeted to varying degrees, demonstrate a complex dynamic of rivalries and alliances. Attacks against these nations could be linked to broader geopolitical issues, diplomatic tensions, or economic rivalries. In the context of the war between Ukraine and Russia, cyberattacks against Denmark, Germany, Lithuania, and Italy may reflect a broader strategy by Russian-speaking actors aiming to weaken Western allies of Ukraine.
Cyberattacks thus become an extension of geopolitical tensions, an arena where actors seek to assert themselves and exert influence in an increasingly interconnected world.
The primary threat actor is NoName057(16): 126 cyberattacks out of 764
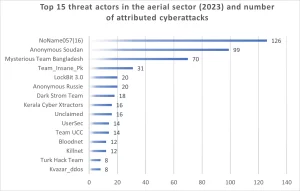
The threat group NoName057(16) is a pro-Russian hacktivist group that has been supporting Russia since March 2022. It operates alongside other groups such as Killnet, sharing similar sympathies towards Russia. NoName057(16) is primarily known for its distributed denial-of-service (DDoS) attacks, a method it has perfected by industrializing the process through a community project called the « DDosia project, » launched on Telegram in early 2022.
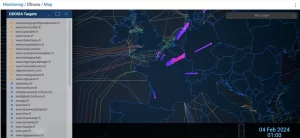
Monitoring of the DDosia project created by the threat group NoName057(16).
During its attacks, the NoName057(16) group primarily targets NATO and EU member countries that actively support Ukraine in the Russo-Ukrainian conflict. Among the notable attacks, the group disrupted Polish government websites after Poland officially recognized Russia as a state supporting terrorism. The Danish financial sector and the websites of candidates in the 2023 Czech presidential election were also targeted.
NoName057(16)’s approach relies on using Telegram to claim responsibility for its attacks and mobilize its supporters. Although the group is not technically sophisticated, its ability to orchestrate DDoS attacks quickly and cohesively demonstrates its effectiveness in disrupting online services. Additionally, the group financially rewards its most active contributors.
To achieve this, the threat group has implemented a cryptocurrency reward system, a practice that reinforces its operating model. This compensation system aims to motivate and reward active participants in the « DDosia project » established by the group.
Finally, the threat posed by NoName057(16) is reinforced by its ability to evolve and diversify its tactics. With a particular focus on countries criticizing Russia’s invasion of Ukraine, the group remains a relative and notably noisy threat in the current geopolitical context.
To go further: The Largest Campaign Recorded
The largest campaign recorded in 2023 against the aviation sector occurred on February 19. Perpetrated by the Mysterious Team Bangladesh group, this campaign took the form of a Distributed Denial of Service (DDoS) attack targeting the websites of twenty-three Swedish airports. The scale of this attack resulted in disruptions to the online services of these companies.
The motivation behind this attack was cited as a reaction to the incident where an Iraqi residing in Sweden had set fire to a copy of the Quran outside the central mosque in Stockholm. The use of the cause « for burning Quran » highlighted how ideological motivations and socio-political events can be exploited as pretexts for cyber attacks.
In summary, the analysis of the cyber threat in the aviation sector for the year 2023 highlights:
- 764 cyber attacks recorded in the aviation sector in 2023
- The majority of attacks are Distributed Denial of Service (DDoS) attacks (679 attacks) followed by ransomware attacks (52 attacks)
- The primary victim country is Sweden (64 attacks), followed by France (56 attacks)
- The main threat actor is NoName057(16): 126 cyber attacks out of 764
- The main targets are airports: 486 out of 764, or 64%

SysDream supports you in managing the cyber risk of your computer system. We provide (whether you are a client or not) a team of experts specialized in incident response and digital forensics to contain a cybersecurity incident, remedy it, and investigate the sources of the attack.
DON’T WAIT TO BE ATTACKED! Contact us.
https://sysdream.com/audit-conseil/ris-reponse-incidents-securite/